SEBI Cyber Security and Cyber Resilience Framework
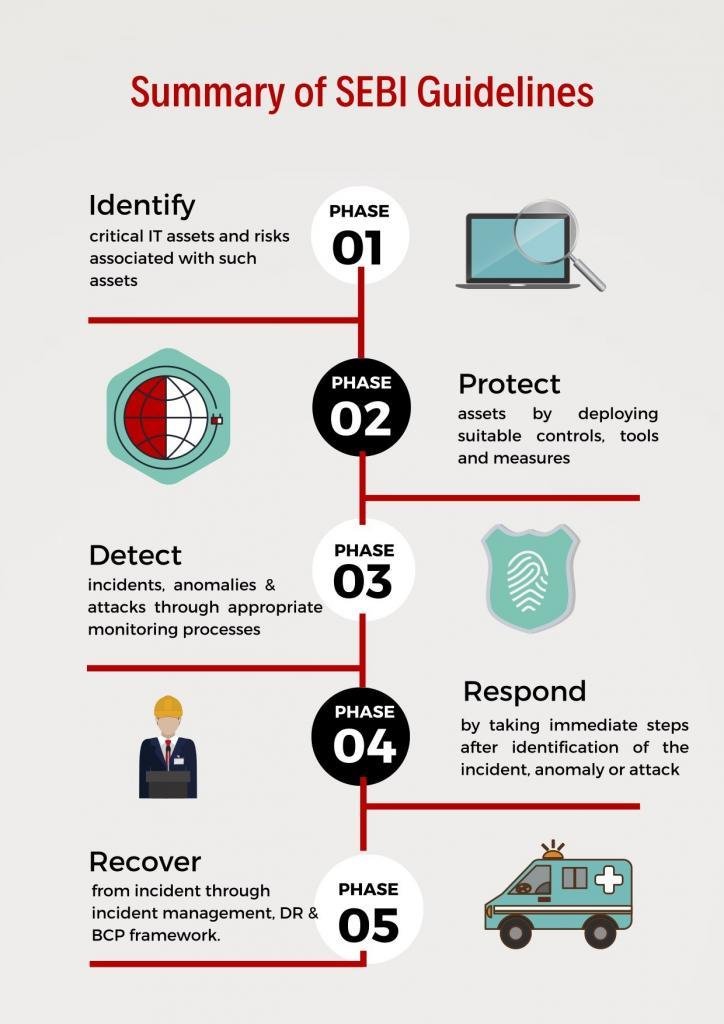
The SEBI Cyber Security and Cyber Resilience Framework (CSCRF) is a set of guidelines issued by the Securities and Exchange Board of India (SEBI) to help regulated entities (REs) protect their information systems and data from cyber threats. The CSCRF covers a wide range of topics.
RNR, as a CERT-In Empaneled Security Auditor, is licensed to assist you in understanding, managing, and complying with SEBI Cyber Security and Cyber Resilience Guidelines that are provided on a regular basis.
SEBI issued guidelines in 2018 and 2019 for a variety of businesses that are within its authority, including Stockbrokers, Depository Participants, Mutual Funds, Asset Management Companies (AMCs), Stock Exchanges, Clearing Corporations, and Depositories.
As an approved security auditor listed by CERT-IN, RNR has the authority to assist you in comprehending, managing, and complying with SEBI’s cybersecurity and cyber resilience guidelines that are regularly published. SEBI has issued guidelines in 2018 and 2019 for various organizations falling under its jurisdiction, including stock brokers, depository participants, mutual funds, asset management companies (AMCs), stock exchanges, clearing corporations, and depositories.
- Dec 03, 2018: SEBI Guidelines for Stock Brokers and Depository Participants.
- Jan 10, 2019, SEBI Guidelines for Mutual Funds / Asset Management Companies (AMCs).
- Dec 07, 2018, SEBI Guidelines for Stock Exchanges, Clearing Corporations and Depositories.
Download Our Whitepaper to learn more about the Cyber Security & Cyber Resilience Framework released for each segment and how RNR can help you comply with SEBI’s mandates.
What we do
RNR provides a comprehensive SEBI CSCRF (SEBI – Cyber Security & Cyber Resilience Framework) that helps organizations improve their cyber security posture and reduce their risk of being attacked. There are step by step procedures that we follow and by using our services, you can improve and understand the CSCRF and implement it effectively.
Contact us to understand more about the Cyber Security & Cyber Resilience Framework, and how RNR may assist you in meeting SEBI’s mandates
What is Application Security?
Effective Security Testing Safeguards your Applications from Cyber Threats & Vulnerabilities
RNR Application Security Testing helps you detect application vulnerabilities, provide full coverage for Web and Mobile application infrastructure and online services, and reduce risks to meet regulatory compliance requirements. Our Application Security Methodology extends beyond scanning software detection to identify and prioritize the most vulnerable aspects of your online application, as well as come up with practical Solutions.
Leave us message

